-
What is machine learning? Understanding its significance and applications
Machine learning (ML) powers many of the apps, online services, and devices people use every day. It enables ride-sharing services, drives personalized recommendations on streaming platforms, and help...
-
Filter bubble explained: How algorithms shape what you see online
Online platforms, including search engines, social media apps, and video-sharing sites, try to show you content that you’re more likely to engage with. This can make the internet feel more relevant,...
-
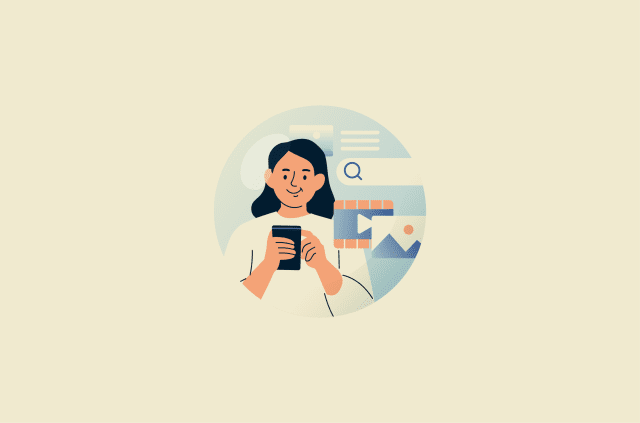
Passphrase vs. password: Which one gives you better security?
It’s easy to assume that any password is enough to protect your accounts, but not all secrets offer the same level of security. While traditional passwords have long been the standard for signing in...
-
How to recover deleted files on iPhone: 7 fast ways that work
Losing a file on your iPhone can feel final, but in many cases, it isn’t. Deleted photos, notes, documents, and other files often remain recoverable for a while. This guide walks you through practic...
-
How to delete your Google Play account safely and protect your data
Your Google account and Play Store profile are important hubs for managing many of the services and apps you use on a daily basis. However, for various reasons, you may wish to decouple a Google accou...
-
Triangulation fraud: How it works and how to prevent it
You order something online, it arrives exactly as promised, and everything seems fine. However, unbeknownst to you, a fraudster has used stolen credit card details to purchase the item, making you an ...
-
Metadata explained: What it is, why it matters, and how to protect it
Metadata is part of many everyday digital activities, from taking photos and sending emails to creating documents and browsing websites. Although it often goes unnoticed, it plays an important role in...
-

Google Shielded Email: What it is and alternatives you can use today
Google was reported in 2024 to be working on a new feature called Shielded Email that would let users create email aliases for sign-ups without revealing their primary address. However, this feature h...
-
What is pretexting in cybersecurity? Definition, examples, and prevention
Understanding how pretexting works and how to recognize it can meaningfully reduce the risk of exposure. This article covers what pretexting is, how it plays out in real-world scenarios, and the pract...
-
How to recover deleted files on Android phone: Fast methods that work
Accidentally deleting files on a phone can remove important data that is hard to replace, from personal memories to work-related documents. Fortunately, there are several ways to recover deleted files...
Featured